Advanced Persistent Threat Security: 5 Modern Strategies
What Is An Advanced Persistent Threat (APT)?
An Advanced Persistent Threat (APT) is a form of cyberattack that involves an attacker gaining unauthorized access to your network and persisting (remaining undetected) for an extended period. The objective of APT attacks is typically to steal valuable data or to disrupt the normal operation of an organization’s network.
APT attacks are commonly executed by well-funded and highly skilled hacker groups, such as nation-state actors or organized criminal organizations. These groups use a combination of tactics, techniques, and procedures to access the target network, establish a foothold, and then move laterally to other parts of the network to gather intelligence and data. APT attacks are difficult to defend against because the attackers can often adapt and evolve their tactics in response to the defenses put in place by the target organization.
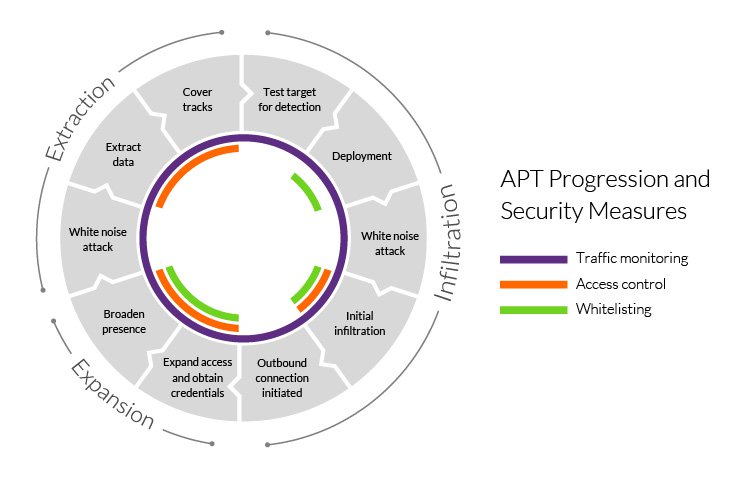
How Advanced Persistent Threats Work
APT attacks are different from traditional cyber threats in a number of ways. First, APT attacks are typically highly targeted and carefully planned. The attackers will often spend a significant amount of time researching their target and gathering intelligence about the network and its defenses before launching the attack. This enables the attackers to tailor their tactics to the specific target and to remain undetected for the longest possible time.
In contrast, traditional cyber threats are often opportunistic and do not require the same level of planning and intelligence gathering. They may use generic malware that is distributed widely in the hopes of infecting as many systems as possible, rather than being tailored to a specific target. Read More…



